
Configuring a VNet-to-VNet VPN Gateway Connection Using the Azure Portal
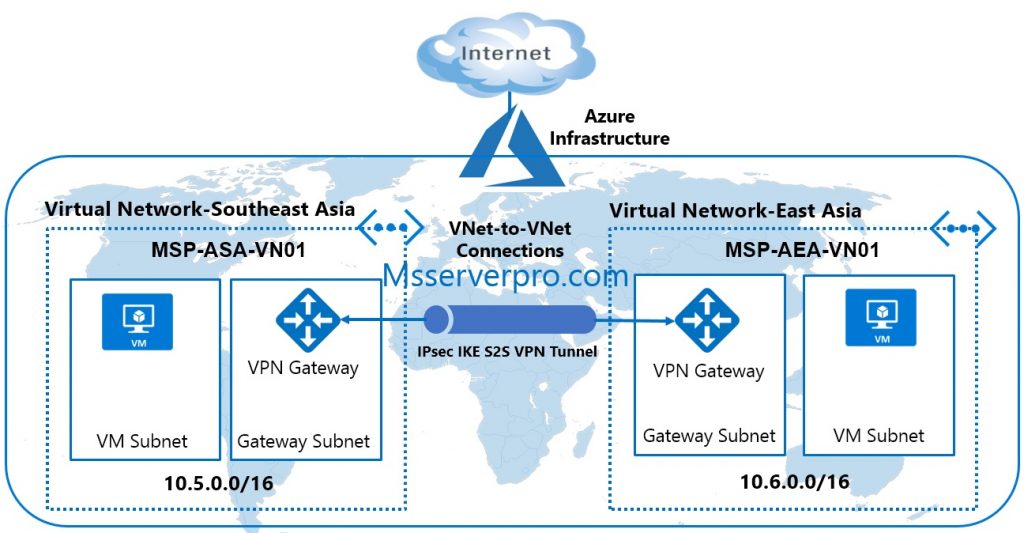
In the previous article, you have configured Azure VNet peering that connects Azure virtual network within the same Azure region through Azure backbone network. This time, you can use a VNet-to-VNet to connect Azure virtual networks in two different Azure regions. Using VNet-to-VNet is similar to a site-to-site VPN. In site-to-site VPN, traffic does traverse the internet but in VNet-to-VNet is routed over a Microsoft Azure backbone network. Configuring a VNet-to-VNet VPN connection is similar to a site-to-site VPN connection with one difference: the other side of the connection is not an on-premises network, but another Azure virtual network. But both connectivity types use a VPN gateway to provide a secure tunnel using IPsec/IKE. VNet-to-VNet communication can be combined with multi-side configuration.
The following procedure outlines the steps to use the Azure portal to create a VNet-VNet-to-VNet VPN connection:
- Create an Azure Resource Group.
- Create a Virtual Network and Add a Gateway Subnet.
- Create a Virtual Network Gateway and Add a Public IP address for Azure VPN Gateway.
- Repeat steps 1-3 to create a second Virtual Network (VNet).
- Create a Connection object that connects the two virtual network gateways.
Step 1: Creating an Azure Resource Group
1. Open your Azure Management Portal at https://portal.azure.com
2. In the portal, click on Resource groups. On the Resource groups blade, click on Add.

3. On the Resource groups blade, type the following values, and then click on the Create button:
- Resource group name: MSSERVERPRO-ASA-RG01
- Subscription: Use the default subscription
- Resource group location: Select your preferred location ( Here, I select Southeast Asia)

4. The Resource Group has been successfully created.

Step 2: Create a Virtual Network and Create a Gateway Subnet
1. In the Hub menu on the left side of the portal page, click New. On the New blade, click Networking. On the Networking blade, click Virtual network.

2. On the Create virtual network blade, specify the following settings, and then click Create:
- Name: MSP-ASA-VN01
- Address space:10.5.0.0/16
- Subscription: select the Azure subscription in which you want to create a virtual network
- Resource group:
- Use existing resource group: MSSERVERPRO-ASA-RG01
- Location: Southeast Asia (The Azure region that is closest to the location and that is available in your subscription)
- Subnet name: BackEnd
- Subnet address range: 10.5.10.0/24

After the virtual network provisioning is complete, you can configure it further by creating additional subnets such as Gateway Subnet and add additional address space and create subnets.
Create a Gateway Subnet:
Before connecting your virtual network to a gateway, you first need to create the gateway subnet for the virtual network to which you want to connect.
1. With the virtual network created, in the Azure portal, click All resources. Click the MSP-ASA-VN01 virtual network in the All resources If the subscription you selected already has several resources in it, you can enter MSP-ASA-VN01 in the Filter by name…box to easily access the VNet.

2. The MSP-ASA-VN01 blade opens and displays information about the VNet. Click Subnetsblade to display a list of the subnets within the VNet. The only subnet that exists is BackEnd, the subnet you created in step 2.

3. In the MSSERVERPRO-VNet – Subnets blade, click + Gateway Subnet to create a Gateway subnet and specify the Address range (CIDR block) and click OKto create the Gateway subnet.



Step 3: Create a Virtual Network Gateway and Add a Public IP address for Azure VPN Gateway
In this step, you can create the Azure Virtual Network Gateway for your Virtual Network. Creating a gateway can often take 45 minutes or more, depending on the selected gateway SKU.
1. In the Hub menu on the left side of the portal page, click New. On the Newblade, click Networking. On the Networking blade, click Virtual network gateway.

2. First you need to give Virtual Network Gateway name: MSP-ASA-GW01. Then extend the Virtual network blade and connect your gateway to the gateway network we previously created in the Virtual Network.

3. Now you need to create a public IP for your gateway. Extend the Public IP address blade and click on Create new.

4. Another blade open and you need to give the new Public IP address a name for the resource and need to save with OK.

5. After you have created the Public IP address, you need to select gateway type you want to use. To deploy a site-to-site VPN based on IPsec, select the gateway type VPN. In the VPN type, select Route-based Most configurations require a Route-based (dynamic routing) VPN type. Then select the gateway SKU from the dropdown.

6. Click Create to begin creating virtual network gateway. The settings are validated and the gateway deploys. Provisioning a virtual network gateway may take up to 45 minutes.


Step 4: Repeat steps 1-3 to Create a Second Virtual Network (VNet), Gateway Subnet, Virtual Network Gateway and Public IP address
Note: The second Virtual Network is created in the different region and different Resource Group.
Resource Group Name: MSSERVERPRO-AEA-RG01
Virtual Network: MSP-AEA-VN01
Virtual Network Gateway: MSP-AEA-GW01
Public IP Address: MSP-AEA-GW01-PIP
Location: East Asia

Steps 5: Configuring Connection between two Virtual Network Gateways
Once the virtual network gateways for both MSP-ASA-VN01 and MSP-AEA-VN01 have completed, you can create your virtual network gateway. Now you need to create connections to enable communications between gateways and enable the routing, by using the same shared key.
1. In All Resources, navigate to the virtual network gateway for your VNet. For example, MSP-ASA-GW01. Click MSP-ASA-GW01 to open the virtual network gateway blade.

2. On the virtual network gateway blade MSP-ASA-GW01, click Connections Click +Add to open the Add connection blade.

3. On the Add connection blade, in the name field, type a name for your connection. For example, MSP-ASA-VN01toMSP-AEA-VN01. For Connection type. Select VNet-to-VNet from the dropdown. The First virtual network gateway field value is automatically filled in because you are creating this connection from the specified virtual network gateway.

4. The Second virtual network gateway field is the virtual network gateway of the VNet that you want to create a connection to. Click Choose another virtual network gateway to open the Choose virtual network gateway Select the virtual network gateway that is listed.

5. You then need to create a Shared key (PSK) secret for both gateway to share. Click OK at the bottom of the blade to save your changes.

6. To set the Connection Status of both networks as Succeeded, you need to repeat the steps. Use the same method that you need to create the connection from MSP-AEA-VN01to MSP-ASA-VN01.

7. In All resources, navigate to the virtual network gateway blade MSP-AEA-GW01, click Connections Click +Add to open the Add connection blade.

8. On the Add connection blade, in the name field, type a name for your connection. For example, MSP-AEA-VN01toMSP-ASA-VN01. For Connection type. Select VNet-to-VNet from the dropdown. The First virtual network gateway field value is automatically filled in because you are creating this connection from the specified virtual network gateway.

9. The Second virtual network gateway field is the virtual network gateway of the VNet that you want to create a connection to. Click Choose another virtual network gateway to open the Choose virtual network gateway Select the virtual network gateway that is listed.

10. You then need to create a Shared key (PSK) secret for both gateway to share. Click OK at the bottom of the blade to save your changes.

11. Verify the connections. For each virtual network gateway, do the following. In All resources, locate the blade for the virtual network gateway, For example, MSP-AEA-GW01.
12. On the virtual network gateway blade, click Connections to view the connections blade for the virtual network gateway. View the connections and verify the status is Updating.

13. After few minutes, you will see Succeeded and Connected as the Status values.


In the Notification, you can see Create connection box, Successfully created connection.

As displayed above, the connection is established. The status of two virtual network gateway MSP-ASA-VN01toMSP-AEA-VN01 is Connected. You can double-click each Connection separately to observe that some amount of Data transferred between these two virtual networks.


The same scenario can also see in the other virtual network gateway MSP-AEA-VN01toMSP-ASA-VN01. The connection is established and data has been transferred between virtual networks.

Summary:
This article shows how to configure VPN to VPN connection between two virtual networks located in two different regions in Azure (Southeast Asia and East Asia). I hope this helps.









nice explain, same article goes for configuration of site to site and express route as well.
Hey i need to establish connection between 2 different subscription and after connect between them need to use azure sql in azure data factory. can you please help me ASAP.